My first rule of security: Simplify
Ships are safe in the harbour
But that is not what ships are built for
[Grace Murray Hopper (December 9, 1906 – January 1, 1992) was an American computer scientist and United States Navy rear admiral. A pioneer in the field, she was one of the first programmers of the Harvard Mark I computer, and developed the first compiler for a computer programming language. She conceptualized the idea of machine-independent programming languages, which led to the development of COBOL, one of the first modern programming languages. She is credited with popularizing the term “debugging” for fixing computer glitches (inspired by an actual moth removed from the computer). Owing to the breadth of her accomplishments and her naval rank, she is sometimes referred to as “Amazing Grace”. The U.S. Navy destroyer USS Hopper (DDG-70) is named for her, as was the Cray XE6 “Hopper” supercomputer at NERSC.]
Courtesy Wikipedia, of course. That ran a tad long, but very impressive and inspiring!
Most of us build ships that are destined to sail on rough seas. Architectures evolve, maps get better, engineering innovates and safety kicks in faster; but there will always be passengers and payload; and thus, there will always be the risks of losing power, running aground, sinking and…pirates. Aside from watching the competition sail by in full view, of course.
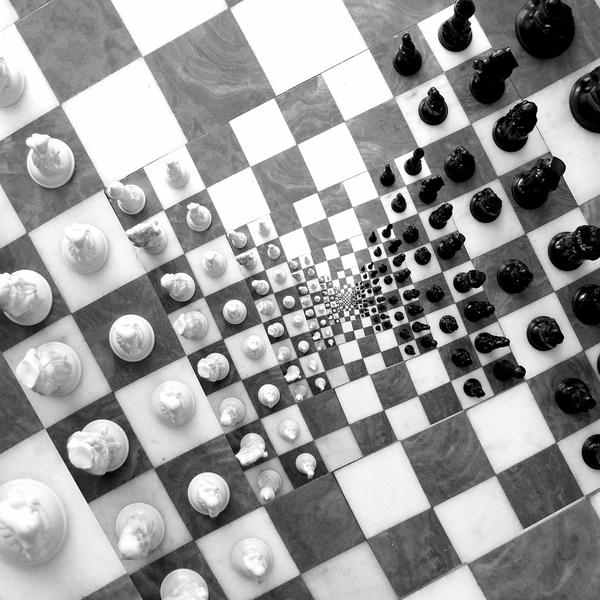
With all those factors, I imagine security would be one of the layers perceived by the average CEO on her / his chessboard…
My Guiding Principles for Security:
- Simplify
- Adapt
- Balance
- Comply
- Enhance
The direction is to engage the company into security by simplifying it as much as possible, adapting it to the markets & technologies we focus on, empowering the company to make informed risk decisions around security, enter new markets and prepare for changes through an appropriate focus on security compliance; and cumulatively enhance our overall offering quality to build trust with the market around our security posture.
- Simplify
- ROI via security for the company in terms of:
- Brand & reputation growth through customer trust
- Strategic growth of offerings, features and services related to security
- Enforcement of security controls to technical leaders and support organizations
- Engagement into security by the workforce, partners and customers through:
- Awareness of security anomalies and alerting protocols
- Role-based training and ad-hoc security assistance
- Intuitive secure data handling
- ROI via security for the company in terms of:
- Adapt
- To market changes around technology adoption, deployment environment and user maturity
- To the consumer side of enterprise technologies
- To pervasive user technology: social, mobile, SaaS
- Balance
- Consumer driven innovation against strategic vision
- Features against direction
- Comply
- Creation of a strong compliance core that can stretch to fit customer needs
- Identification of strategic partners and attestations to strengthen the brand
- Enforce core tenets of confidentiality to encompass all stakeholder data
- Enhance
- Quality by enforcing security in the SDLC and the ability to measure security defects
- Identity through redundant channels to validate user & machine entitlements
- Risk management & audit-friendliness through transparent, robust controls































Vox Populi