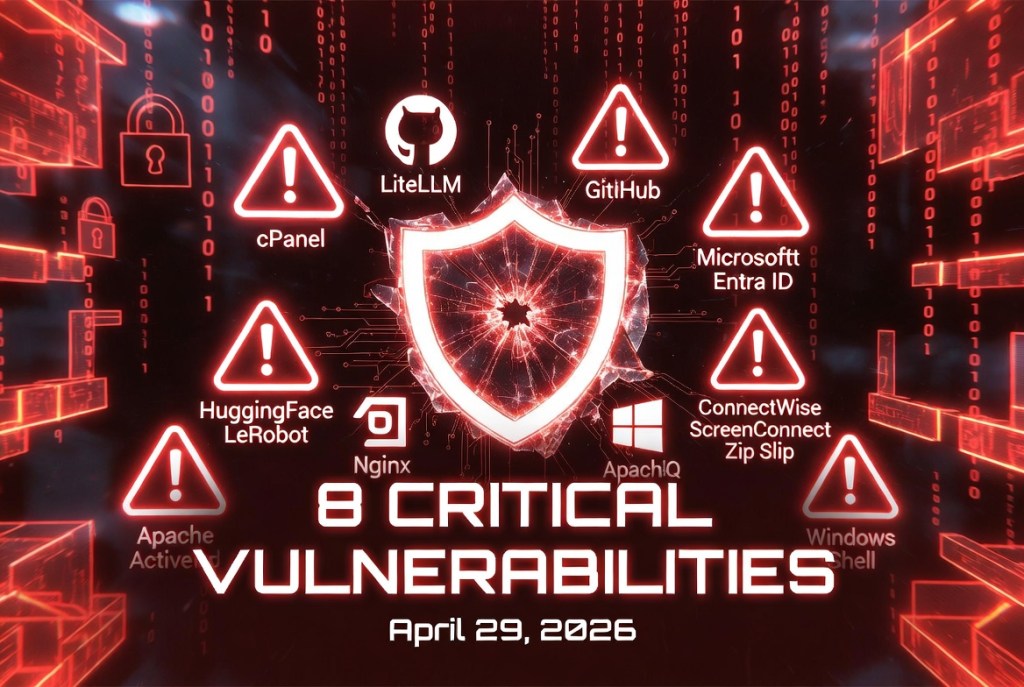
cPanel authentication vulnerability — Affects login paths. This affects all versions, and is fixed only for the following versions:
- 11.110.0.97
- 11.118.0.63
- 11.126.0.54
- 11.132.0.29
- 11.136.0.5
- 11.134.0.20
Update immediately – https://support.cpanel.net/hc/en-us/articles/40073787579671-cPanel-WHM-Security-Update-04-28-2026
LiteLLM SQL injection vulnerability – CVE-2026-42208 – Critical (CVSS 9.3)– This is a vulnerability in the popular LLM gateway. It has started to be actively exploited in the wild within 36 hours of disclosure via crafted authorization headers.
GitHub Remote Code Execution vulnerability – CVE-2026-3854 – High (CVSS 8.7) – Command injection via single crafted git push; exploitable by any authenticated user with push access.
Microsoft Entra ID Agent ID Administrator role flaw — Enables privilege escalation and arbitrary service principal takeover. Details at the excellent write-up by Silverfort’s Noa Ariel.
nginx-ui – CVE-2026-33032 – Critical [CVSS 9.9). Actively exploited. It allows full Nginx server takeover. The Rapid7 writeup also explains the chain with CVE-2026-27944 and how a Model Context Protocol server can be accessed to perform privileged operations on managed Nginx web servers.
Hugging Face LeRobot Remote Code Execution vulnerability – CVE-2026-25874 – Critical [CVSS 9.3). This is an unpatched critical deserialization flaw via pickle over gRPC. This affects PolicyServer and robot clients (v0.4.3). As of now, the planned fix is only for version v0.6.0. Details evolving.
Aside from the possible theft of API keys / SSH credentials, this could also compromise robot behavior. Without TLS and without authentication, attackers can send malicious payloads.
New additions to the CISA Known Exploited Vulnerabilties’ Catalog:
Apache ActiveMQ – CVE-2026-34197 – High (CVSS 8.8) — Actively exploited. An authenticated attacker can exploit this vulnerability by sending a specially crafted discovery Uniform Resource Identifier (URI) to the Jolokia JMX-HTTP bridge, which is exposed on the web console. This allows the attacker to bypass configuration validation and load a remote Spring XML application context. Consequently, this leads to arbitrary code execution on the broker’s Java Virtual Machine. This applies to Apache ActiveMQ Broker and Apache ActiveMQ.
ConnectWise ScreenConnect “Zip Slip” vulnerability – CVE-2024-1708 – High (CVSS 8.4). This flaw enables attackers to manipulate file paths, potentially gaining unauthorized access to files or directories located outside the intended restricted directory. It was reported on February 19, 2024 alongwith another authentication bypass vulnerability – CVE-2024-1709.
Windows [Shell] protection failure – CVE-2026-32202 – Medium (CVSS 4.3) — Path traversal Remote Code Execution and spoofing flaws now known to be actively exploited. Akamai’s Maor Dahan indidated that this represents an incomplete remediation of CVE-2026-21510. While the earlier patch mitigated remote code execution risks, it failed to fully address underlying mechanisms that could still be abused.


Leave a comment